SEC 340 Week 2 Quiz 1
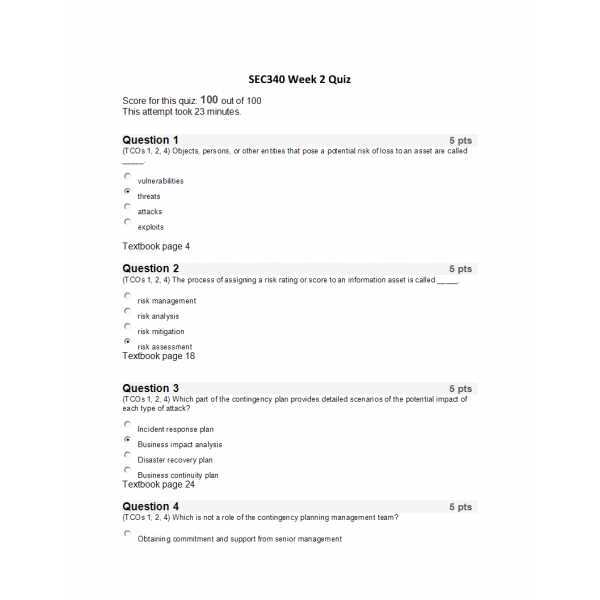
SEC 340 Week 2 Quiz
1. (TCOs 1, 2, 4) Objects, persons, or other entities that pose a potential risk of loss to an asset are called _____.
2. (TCOs 1, 2, 4) The process of assigning a risk rating or score to an information asset is called _____.
3. (TCOs 1, 2, 4) Which part of the contingency plan provides detailed scenarios of the potential impact of each type of attack?
4. (TCOs 1, 2, 4) Which is not a role of the contingency planning management team?
5. (TCOs 1, 2, 4) Threats are converted to attacks and then used to create attack ______.
6. (TCOs 1, 2, 4) Which of the following is a method or source for collecting data for the BIA?
7. (TCOs 3, 5) Which of the following is not a possible IR team structure model?
8. (TCOs 3, 5) The circumstances that cause the IR plan to be initiated are called the _____.
9. (TCOs 3, 5) Which type of plan testing involves individuals who act as if an incident has occurred, but do so without interfering with normal operations?
10. (TCOs 3, 5) Legitimate activities wrongly reported as incident candidates are referred to as _____.
11. (TCOs 3, 5) The _____ should be the first deliverable undertaken by the IR planning committee.
12. (TCOs 3, 5) Which of the following is required first and foremost for the successful execution of a business continuity plan?
13. (TCOs 3, 5) _____ reflect upon the relative security of an information system.
14. (TCOs 3, 5) Which of the following refers to the way that an information system is capable of identifying those who do not have the right to know and access information?
15. (TCOs 3, 5) Which of the following is not a problem associated with risk management?
16. (TCO 1) The _____ model of information security evolved from a concept known as the CIA triangle.
17. (TCO 1) Which of the following can become the basis for an attack on information?
18. (TCOs 2, 4) The BIA takes up where the _____ leaves off.
19. (TCO 5) When a non-event is categorized as an actual incident, it is also known as a _____.
20. (TCO 5) False positives or noise often result from which of the following causes in an incident collection candidate?
| Institution & Term/Date | |
| Term/Date | Devry Keller |
-
$12.00