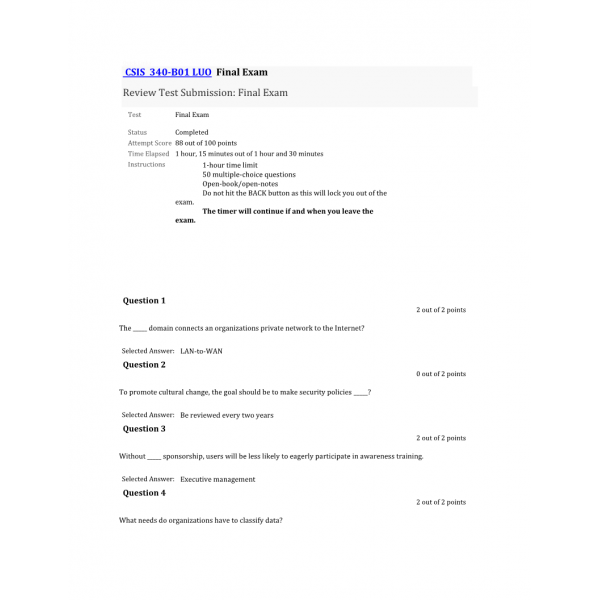
CSIS 340 Final Exam LUO
CSIS 340 Final Exam
1. The _____ domain connects an organizations private network to the Internet?
2. To promote cultural change, the goal should be to make security policies _____?
3. Without _____ sponsorship, users will be less likely to eagerly participate in awareness training.
4. What needs do organizations have to classify data?
5. The Security Compliance Committee _____?
6. Web Services policies would be an example of _____ domain.
7. Production data should be _____ before being used in a test environment?
8. Which of the following includes guidelines under the LAN domain policies?
9. Which of the following is a common cause of security breaches?
10. What is a strong indicator that awareness training is not effective?
11. Baseline standards for the LAN domain would include _____.
12. Which of the following is not an organizational challenge when implementing security policies?
13. The ______________ model was the first model developed to address the concerns of integrity. Originally published in 1977
14. _____ occurs when you manipulate or trick a person into weakening the security of an organization?
15. Data in transit refers to what type of data?
16. Simple security policy awareness requires that _____ report suspicious activity?
17. A business impact analysis requires an impact report, component reliance, and a _____.
18. _____ techniques can provide a security baseline for full operating systems and applications?
19. A _____ standard describes the requirements for obtaining a domain name for use by external parties?
20. A(n) _____ has an easier time bypassing security controls and hiding his or her tracks by deleting or altering logs and time stamps.
21. _____ typically have the technical skills to make critical recommendation on how to stop an attack.
22. Why should a security policy implementation be flexible to allow for updates?
23. Two-factor authentication is a typical control used by employees to remotely access which of the following?
24. It is necessary to retain data for what major reasons?
25. A _____ is the first step in building a business continuity plan (BCP) to minimize losses.
26. Security policy enforcement can include _____?
27. _____ protects data at rest from all type of breaches.
28. Once security policies are established, line management must _____ ?
29. Outdated application controls place a greater reliance on _____?
30. The following documents help capture domain security control requirements?
31. The ________________ model uses mandatory access control to enforce the DoD multilevel security policy.
32. Generally, an Acceptable Use Policy should outline _____?
33. A _____ is a specialized group of people whose purpose is to respond to major incidents.
34. Which of the following should be in an information response team charter?
35. A(n) ______ ensures workers are conscious of security risks and how to deal with unexpected risk.
36. Without a policy that leads to controls that restrict employees from installing their own software on a company workstation, a company could suffer which of the following consequences?
37. Good reasons to monitor worker’s computer activities are when ______?
38. A _____ is a common control that is used across a significant population of systems?
39. Employer response to an employee posting company passwords on their social network site should include _____?
40. Security experts consider _____ the weakest link in security.
41. A malicious _____ attack uses viruses, worms, Trojan horses, and scripts to gain access to systems, applications, and data.
42. You can use a _____ process to grant temporary elevated rights.
43. The following organization has offered reliable security policies in the past to help organizations develop proper infrastructure policies.
44. _____ are especially useful for identifying unauthorized changes.
45. The Risk Management Continuous Improvement Model includes _____?
46. The signs of an incident can be _____?
47. _____ determines how quickly a business process should be recovered.
48. A privileged-level access agreement (PAA) is designed to heighten the awareness and accountability of?
49. ______ software is capable of capturing usernames, passwords, and websites visited on a local workstation?
50. A _____ can identify hosts on a network and determine services running on the hosts.
| Institution & Term/Date | |
| Term/Date | Liberty University |
-
$30.00